Exploring Effective Strategies for Combating Wormhole Attacks in Wireless Ad Hoc Networks
Within the vast and intricate world of wireless ad hoc networks, a particularly devious form of security threat lurks – the wormhole attack. This form of attack targets the routing layer of the network, bypassing even the most robust cryptographic defenses and potentially crippling the entire communication framework. Given the inherent difficulty in preempting such attacks, the development of effective countermeasures has been both a critical challenge and a focal point of research in network security.
The conundrum lies not just in the detection of these wormhole attacks but also in the cost and practicality of potential solutions. Prevailing strategies often necessitate either the deployment of prohibitively expensive hardware or the imposition of restrictions on adversarial behavior, neither of which offer a comprehensive or feasible long-term remedy.
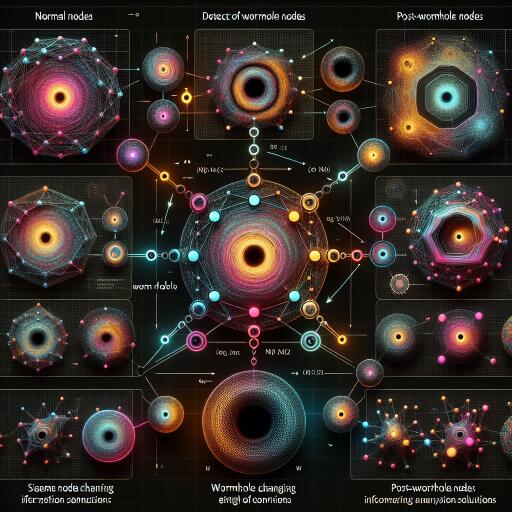
In response to this, a novel approach has been proposed, one that eschews the need for additional hardware or alterations to the network infrastructure. This strategy pivots on a heuristic model designed to identify and isolate wormhole nodes based on their suspicious post-attack behaviors, such as packet dropping, manipulation of packet life time, and unauthorized packet looping, among others.
The crux of this innovative solution is its reliance on existing network protocols, paired with a keen analysis of malicious node behavior post-wormhole creation. Simulation studies, conducted using the ns2.30 platform, have underscored the efficacy of this approach, showcasing detection rates soaring between 98-99% and an impressively swift average detection and isolation time of just 0.67 seconds. While the approach introduces an overhead of 22%, it stands out for its adaptability to both static and mobile scenarios, with a marked increase in performance and reliability over existing methodologies.
Wireless ad hoc networks, characterized by their decentralization, dynamic topology, and lack of fixed infrastructure, are pivotal in a variety of contexts, ranging from military operations and disaster recovery to the burgeoning fields of the Internet of Things (IoT) and ad hoc cloud computing. However, the open nature of these networks also renders them especially vulnerable to a spectrum of cyber threats, with wormhole attacks posing one of the most formidable challenges.
A wormhole attack exploits the network’s inherent shortest path routing protocols, creating an illusion of the optimal route through colluding nodes, thereby disrupting the flow of data. AODV (Ad Hoc On-demand Distance Vector), a widely utilized routing protocol within these networks, has been identified as particularly susceptible to such attacks due to its design and operational mechanisms.
The proposed solution, distinguished by its lack of reliance on additional hardware or network modifications, leverages the AODV protocol to identify and mitigate the effects of wormhole attacks. By monitoring and analyzing network behavior for indications of wormhole-related activities, this approach enables the swift detection and isolation of malicious nodes, significantly bolstering network security and resilience.
Moreover, the proposed methodology offers a profound insight into the nature and mechanisms of wormhole attacks, drawing a clear distinction between pre-attack vulnerabilities and post-attack behaviors, thereby enabling more targeted and effective intervention strategies. While the focus of current research has been predominantly on the detection of such attacks, the quest for a holistic defense mechanism that encompasses both detection and prevention remains a critical objective for the cybersecurity community.
In conclusion, the advancement of a heuristic-based solution for the detection and isolation of wormhole attacks in wireless ad hoc networks marks a significant step forward in the ongoing battle against cyber threats. By leveraging the inherent characteristics of the network’s routing protocol, combined with a systematic analysis of post-attack behaviors, this approach offers a viable and effective strategy for safeguarding the integrity and functionality of these critical communication networks. As research continues to evolve in this domain, it is hoped that further refinements and innovations will pave the way for even more robust and resilient security mechanisms.